- Home
- Bog
How Offensive and Defensive Security Work Together, The Complete Cyber Defense Model

How Offensive and Defensive Security Work
In today’s cyber battlefield, organizations are constantly under threat from ransomware syndicates and insider risks to zero-day vulnerabilities. Yet, too often, businesses focus solely on defense: firewalls, EDRs, and SIEM systems. While these are essential, true resilience demands balance.
The strongest security posture comes from integrating Offensive and Defensive Security, a model that not only reacts to attacks but anticipates them. This is the foundation of CyberHelm’s complete cyber defense philosophy.
What Is Offensive Security?
Offensive Security is proactive. It mirrors the mindset of attackers to uncover weaknesses before adversaries exploit them. The goal is to simulate real-world breaches, evaluate system robustness, and expose vulnerabilities that could lead to data compromise.
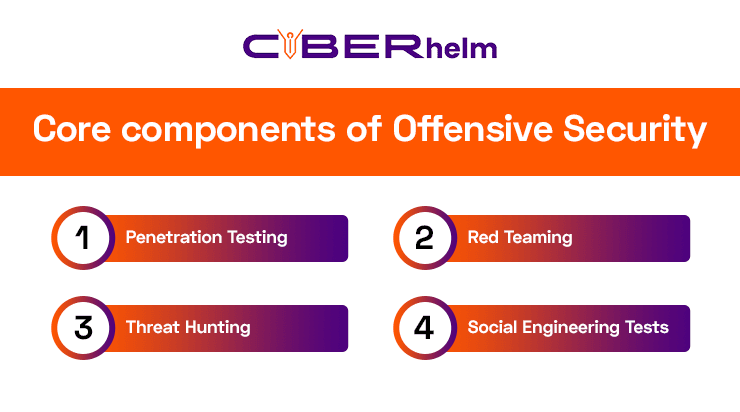
Core components of Offensive Security include:
- Penetration Testing: Controlled attacks that assess how your defenses hold up.
- Red Teaming: Simulated threat campaigns that mimic sophisticated adversaries.
- Threat Hunting: Identifying hidden threats and lateral movements before detection tools trigger alerts.
- Social Engineering Tests: Evaluating human vulnerabilities, the weakest link in many cyber incidents.
Through these tactics, enterprises gain a realistic understanding of their exposure and can strengthen their defenses accordingly.
For example, AI-powered systems can monitor network traffic 24/7 and immediately detect anomalies—like an unexpected data transfer or unauthorized login attempt. These systems continuously learn from each interaction, becoming smarter and more effective over time.
What Is Defensive Security?
Defensive Security is the reactive and protective layer. It ensures that when a breach attempt occurs, it’s detected, contained, and neutralized quickly. Defensive measures focus on continuous monitoring, response orchestration, and resilience building.
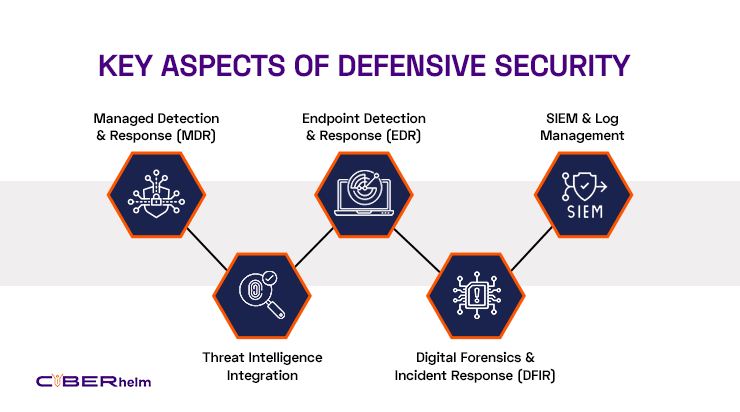
Key aspects of Defensive Security include:
- Managed Detection & Response (MDR)
- Endpoint Detection & Response (EDR)
- SIEM & Log Management
- Digital Forensics & Incident Response (DFIR)
- Threat Intelligence Integration
Together, these create a cyber immune system, one that not only responds to threats but learns and evolves from them.
The Power of Integration: Red + Blue = Purple Teaming
When Offensive (Red Team) and Defensive (Blue Team) units collaborate, you achieve Purple Teaming, a continuous feedback loop that bridges the gap between attack and defense.
This synergy enables organizations to:
- Detect gaps in monitoring and detection strategies.
- Validate incident response readiness.
- Accelerate remediation and improve team coordination.
- Create a culture of proactive defense and real-time learning.
It’s the most efficient way to transform cybersecurity from reactive firefighting to strategic foresight.
Why This Matters More Than Ever
Modern threats evolve faster than ever. Traditional defenses alone can’t keep up with AI-driven attacks, supply chain compromises, and cloud vulnerabilities.
An integrated approach helps organizations:
- Predict threats before they strike.
- Prevent costly breaches through continuous testing.
- Protect data, infrastructure, and brand reputation with real-time monitoring.
CyberHelm’s Integrated Cyber Defense Model
At CyberHelm, we don’t separate offense and defense; we unify them.
Our Comprehensive Cyber Defense Framework includes:
- Offensive Security Services for vulnerability discovery.
- Defensive Security & MDR Operations for 24/7 protection.
- Threat Intelligence & Dark Web Monitoring for early warning.
- GRC as a Service for compliance and governance alignment.
By merging human expertise with automation and intelligence, CyberHelm helps clients anticipate, adapt, and overcome the most advanced threats.
Compliance & Governance
Stay future-ready, explore how AI, automation, and innovation are redefining cybersecurity.
Conclusion: One Strategy, Two Forces, Infinite Protection
A resilient cyber posture isn’t built on walls; it’s built on visibility, collaboration, and continuous improvement. When offense informs defense and defense strengthens offense, your organization becomes truly unbreakable.
CyberHelm empowers enterprises and governments with the complete cyber defense model, where every attack becomes an opportunity to grow stronger.
Categories
- Network Security
- Threat Detection
- AI & Automation
- Compliance
- Industry News
Related Posts
Book a Free Consultation
CyberHelm’s Managed Security delivers cutting-edge protection with expert oversight. We provide 24/7 monitoring, threat intelligence, and proactive defense so your team can focus on growth while we handle security
Call Now
0800 7870200